How to Prevent Phishing and Protect Your Brand’s Reputation
In today’s digital age, the threat of phishing is a looming and ongoing concern for brands of all sizes. Phishing attacks have evolved beyond traditional security solutions, requiring brands to take serious steps toward establishing anti-phishing solutions that can keep up with the relentless fraudsters. In fact, it’s no longer enough to set up internal anti-phishing protections, brands are now having to go on offense to protect their brands outside of the firewall.
In this blog, we outline the various types of phishing attacks, the difference between internal and external phishing protection, the adverse effects they can have on your business, and most importantly, the options you have for protecting your brand from falling victim to phishing attacks.
Internal and External Phishing Protection
“Phishing” is a term for cyberattacks that use malicious emails, text messages, and websites designed to trick recipients into providing sensitive information, such as login credentials, financial data, or personal details. This can lead to identity theft, financial loss, and damage to a company’s reputation. Phishing attacks typically employ various psychological and social engineering techniques to manipulate the victim’s trust and induce them to take actions that benefit the attacker.
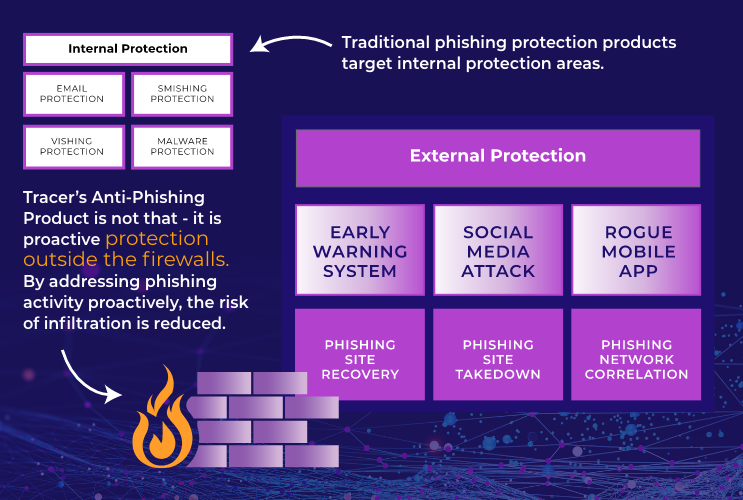
When people think about phishing attacks, they are typically thinking about internal phishing attacks, which happen inside of the firewall. These attacks occur through employee email, phones, and company software being infiltrated by attackers, so protections are set up inside of the firewall. In today’s world, phishing can have an impact on your business outside of your firewall, through fraudulent social media, mobile apps, and websites using your name and likeness to phish. This requires a different kind of anti-phishing protection strategy. There are various advanced threat detection, digital risk protection, and phishing brand protection strategies that can be employed to combat these attacks.
Understanding the Phishing Threat
Phishing is a multifaceted threat, with cybercriminals employing a variety of tactics to deceive individuals and infiltrate organizations. Here are 11 common types of phishing attacks:
-
- Domain Spoofing
-
- Social Engineering Phishing
-
- Mobile App Impersonation
-
- Search Engine Phishing
-
- Email Phishing
-
- Spear Phishing
-
- Whaling
-
- Pharming
-
- Angler Phishing
-
- Vishing
-
- Smishing
Phishing Attack #1: Domain Spoofing
Domain spoofing is when attackers create fake websites that mimic legitimate ones to steal sensitive information.
Phishing Attack #2: Social Engineering Phishing
Social engineering phishing is when bad actors manipulate individuals into revealing confidential information through psychological manipulation.
Phishing Attack #3: Mobile App Impersonation
Mobile app impersonation is when fake versions of popular mobile apps are created to trick users into downloading malicious software.
Phishing Attack #4: Search Engine Phishing
Search engine phishing is when search results are manipulated to redirect users to fraudulent websites.
Phishing Attack #5: Email Phishing
Email phishing is when fraudsters send deceptive emails that appear legitimate to get recipients to share sensitive information.
Phishing Attack #6: Spear Phishing
Spear phishing is when phishing attempts are customized for specific individuals or organizations to increase the chances of success.
Phishing Attack #7: Whaling
Whaling targets high-profile individuals within an organization, such as CEOs or top executives.
Phishing Attack #8: Pharming
Pharming is the practice of redirecting website traffic to fraudulent sites without users’ knowledge.
Phishing Attack #9: Angler Phishing
Angler phishing exploits compromised websites or social media accounts to lure victims into phishing traps.
Phishing Attack #10: Vishing
Vishing is when voice communication is used to deceive individuals into revealing sensitive information.
Phishing Attack #11: Smishing
Smishing is a phishing attack conducted via text messages or SMS.
Effects of Brand Impersonation and Phishing
Loss of Customer Trust and Damage to Brand Reputation
First and foremost, brand impersonation and phishing attacks erode customer trust and tarnish a brand’s reputation. When customers fall victim to phishing attacks posing as legitimate interactions with your brand, it not only leads to compromised personal information and financial losses for the affected individuals, but also damages the trust they have in your company. Brands can suffer significant reputational damage, which can be challenging to repair, as customers may subconsciously associate their negative experience with your brand and be hesitant to engage with you again. In fact, 72% of customers will switch brands after just one bad experience. Customer trust and brand reputation take a lot of time and effort (not to mention money) to build and maintain, but can be lost in an instant.
Loss of Business Revenue
Financial losses are another major consequence of brand impersonation and phishing attacks. These attacks can lead to direct financial theft, such as fraudulent transactions, unauthorized access to bank accounts, or theft of funds through digital payment fraud. Moreover, the costs associated with investigating and mitigating the attack, as well as potential legal liabilities, can further strain a company’s financial resources. Small businesses, in particular, may find it challenging to recover from such financial setbacks, and in some cases, these attacks can lead to bankruptcy.
Operational Disruptions
Beyond financial and reputational damage, brand impersonation and phishing attacks can disrupt normal business operations. Employees may be tasked with addressing the aftermath of an attack, diverting their attention away from core tasks and adding to already busy workloads. Additionally, the spread of malware through these attacks can lead to data breaches, system outages, and compromised intellectual property, causing significant operational disruptions and additional costs for recovery and future threat detection and digital risk protection enhancements.

How to Protect Your Business from Phishing
Establishing a comprehensive phishing brand protection strategy is important for brands to safeguard their reputation, assets, and customer trust. Because brand impersonation and phishing attacks have become increasingly sophisticated, affecting your brand both internally and externally, brands should be proactive in adopting anti-phishing solutions into their digital risk protection strategy to mitigate risks and maintain brand integrity.
Develop a Brand Protection Strategy
Domain Protection:
Registering domain names that are closely associated with your brand and its variants can prevent cybercriminals from setting up fraudulent websites or email addresses to impersonate your brand. Additionally, implementing domain monitoring services can help detect unauthorized domain registrations and take swift action to secure them. Regularly reviewing and renewing domain registrations is crucial to maintain control and prevent domain misuse.
Social Media Monitoring:
Monitoring social media channels for mentions of your brand, both legitimate and fraudulent, is essential. Employing advanced social media monitoring tools can help identify and report fake profiles, phishing attempts, and counterfeit product listings. Rapid response to such incidents can prevent misinformation from spreading and protect your brand’s image.
Monitor Brand Presence Online:
Monitoring your brand’s presence online involves actively searching for websites, forums, and marketplaces where your brand is mentioned. By monitoring and detecting fraudulent uses of your brand across online platforms, you can find counterfeit goods, unauthorized sellers, or misleading content, and then take action to protect your brand’s intellectual property.
Use DMARC:
Implementing Domain-based Message Authentication, Reporting, and Conformance (DMARC) can help authenticate your brand’s email communications with your customers. DMARC ensures that only legitimate emails sent from your domain reach recipients’ inboxes, reducing the risk of phishing attacks. It also provides insights into email fraud attempts, enabling you to take corrective measures swiftly.
Effective Take-Down:
Monitoring isn’t enough, brands have to take efficient and coordinated actions to take down phishing threats. This involves reporting fraudulent websites, social media accounts, and other instances of brand impersonation to the appropriate authorities and platforms. Timely and persistent efforts in pursuing legal action against counterfeiters and impersonators can deter potential threats and enforce brand protection measures.
Leverage Security Technology
Protecting your business from phishing attacks can be time-consuming, resource-draining, and expensive, especially if you’re trying to handle it manually. Phishing brand protection technology can help automate and streamline the process, saving your business time, effort, and money.
Tracer’s Anti-Phishing Solution leverages the power of artificial intelligence and machine learning to detect in real-time even the most sophisticated phishing attempts, across all channels where your brand and customers interact. 98% of anti-phishing and scam sites go undetected by conventional external domain tracing. Where most phishing protection products target internal protection areas only, Tracer’s solution proactively protects your brand outside of your firewall, stopping the attack from infiltration your system in the first place. When a threat is found, Human-in-the-Loop AI uses recursive discovery to look at similar patterns and identify a wider network of attacks, allowing us to find up to 25x more detections. Learn more about Tracer’s Phishing Brand Protection offerings.
“Using the Adaptive Discovery Engine, Tracer can find up to 25x more sites similar to a HITL-verified phishing site for targeted brands”.
– Kyle Mulder, Group Product Manager, Tracer
Conclusion
By investing in robust digital risk protection and anti-phishing solutions, brands can fortify their defenses against phishing attacks and safeguard their sensitive data, finances, and reputation both internally and externally in an increasingly hostile digital landscape.
Author


